Thursday, June 11, 2020
BruteSpray: A Brute-forcer From Nmap Output And Automatically Attempts Default Creds On Found Services
About BruteSpray: BruteSpray takes nmap GNMAP/XML output or newline seperated JSONS and automatically brute-forces services with default credentials using Medusa. BruteSpray can even find non-standard ports by using the
-sV inside Nmap.sudo apt install brutesprayFor Arch Linux user, you must install Medusa first:
sudo pacman -S medusaAnd then, enter these commands to install BruteSpray:
Supported Services: ssh, ftp, telnet, vnc, mssql, mysql, postgresql, rsh, imap, nntpp, canywhere, pop3, rexec, rlogin, smbnt, smtp, svn, vmauthdv, snmp.
How to use BruteSpray?
First do an Nmap scan with
-oG nmap.gnmap or -oX nmap.xml.Command:
python3 brutespray.py -hCommand:
python3 brutespray.py --file nmap.gnmapCommand:
python3 brutesrpay.py --file nmap.xmlCommand:
python3 brutespray.py --file nmap.xml -iYou can watch more details here:
Examples
Using Custom Wordlists:
python3 brutespray.py --file nmap.gnmap -U /usr/share/wordlist/user.txt -P /usr/share/wordlist/pass.txt --threads 5 --hosts 5Brute-Forcing Specific Services:
python3 brutespray.py --file nmap.gnmap --service ftp,ssh,telnet --threads 5 --hosts 5Specific Credentials:
python3 brutespray.py --file nmap.gnmap -u admin -p password --threads 5 --hosts 5Continue After Success:
python3 brutespray.py --file nmap.gnmap --threads 5 --hosts 5 -cUse Nmap XML Output:
python3 brutespray.py --file nmap.xml --threads 5 --hosts 5Use JSON Output:
python3 brutespray.py --file out.json --threads 5 --hosts 5Interactive Mode:
python3 brutespray.py --file nmap.xml -iData Specs
{"host":"127.0.0.1","port":"3306","service":"mysql"}
{"host":"127.0.0.10","port":"3306","service":"mysql"}
...Changelog: Changelog notes are available at CHANGELOG.md.
- BruteDum: Brute Force attacks SSH, FTP, Telnet, PostgreSQL, RDP, VNC with Hydra, Medusa and Ncrack
- FTPBruter: A FTP Server Brute forcing tool written in Python 3
- Blazy - Crack Website Logins in seconds with Bruteforce attacks
- SocialBox: A Bruteforce Attack Framework for Social Networks
- Ncrack: An High-speed Open-source Network cracking tool
- Medusa: A Speedy, Parallel And Modular Login Brute-forcing Tool
Read more
- Pentest Linux
- Pentest Tools Framework
- Hacking Ethics
- Pentest Tools Framework
- Pentest As A Service
- How To Pentest A Network
- Hacking Box
- Pentest Usb
- Hacking Forums
- Pentest +
- Pentestlab
- Pentest Software
- Hacking Site
- Hacking Images
- Pentestgeek
- Pentest Plus
- Pentest Online Course
- Hacking With Raspberry Pi
- Hacking For Dummies
- Pentest Process
Wednesday, June 10, 2020
Exploit-Me
 "Exploit-Me is a suite of Firefox web application security testing tools designed to be lightweight and easy to use. The Exploit-Me series was originally introduced at the SecTor conference in Toronto. The slides for the presentation are available for download. Along with this SecTor is making the audio of the talk available." read more...
"Exploit-Me is a suite of Firefox web application security testing tools designed to be lightweight and easy to use. The Exploit-Me series was originally introduced at the SecTor conference in Toronto. The slides for the presentation are available for download. Along with this SecTor is making the audio of the talk available." read more...Website: http://securitycompass.com/exploitme.shtml
Related links
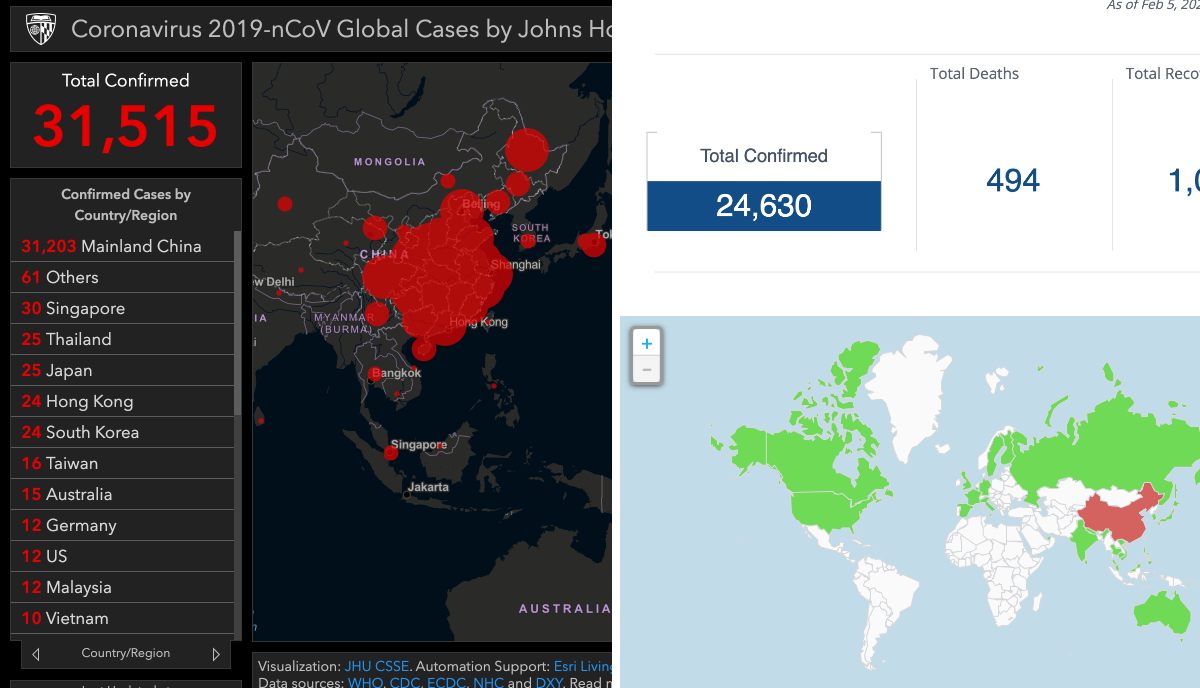
How Block Chain Technology Can Help Fight Wuhan Corona Virus Outbreak
As the death toll and the infected cases of widespread coronavirus continue to increase, global organizations and the tech industry has come forward with technology like blockchain to fight coronavirus.
Along with the equipment and monetary support, technology also withstands against the virus with better plans and solutions. Hence, tech industries have started leveraging blockchain technology in the wake of a global health emergency.
Blockchain Helps In Real-Time Online Tracking
The Center for Systems Science and Engineering has already set up an online platform to track coronavirus and visualize the growing number of infected patients in real-time.
But Acoer, an Atlanta-based blockchain app developer, has also launched an alternative online data visualization tool to easily trail and depict the Cororanvirus outbreak using blockchain technology.
Acoer platform, named HashLog, is more advanced and clear as it pulls the data from the Hedera Hashgraph database using the HashLog data visualization engine.
Hedera Hashgraph is an immutable, transparent and decentralized database based on distributed ledger technology that provides synchronized and unchangeable data from the public networks.
Moreover, researchers, scientists, and journalists can use the HashLog dashboard to understand the spread of the virus and act against it swiftly.
For data sources, Johns Hopkins CSSE extracts data from WHO, CDC, ECDC, NHC, and DXY. On the other hand, Acoer maps the public data, including data from the Center for Disease Control (CDC) and the World Health Organization (WHO). Therefore, data may differ on both platforms.
Blockchain Can Help Monitor And Control Money Flow
To fight the further spread of the coronavirus (2019-nCoV) outbreak globally, China has also received abundant monetary support from the international community to create better action plans.
China's govt-led organization and charities are responsible for overseeing and utilizing the influx of money to research and generate a solution for coronavirus. But due to the lack of coordination and mismanagement among the various organization, money is not being laid out to curb the crisis.
Recently, a paper published by Syren Johnstone, from the University of Hong Kong, discusses the problems encountered by charities, in China and elsewhere. It argues that the present crisis should be seen as a call to arms.
Syren urges for a borderless solution with better management of donations and implementation using the emerging tech like Blockchain and Artificial Intelligence.
Keeping that in mind, Hyperchain, a Chinese company, also announced blockchain-based charity platform to streamline the donation from all over the world.
Since the Hyperchain platform is based on the blockchain, it offers more transparency among the sender and receiver of funds to bring trust and immutability to restrict the transaction data deletion.
Overall, Hyperchain improves administrative function for the money and also extends the logistics actions.
@HACKER NT
Related posts
- Hacker Box
- Hacking Groups
- Pentest Network
- Hacking For Dummies
- Hacker Typer
- Pentest Smtp
- Pentest Training
- Rapid7 Pentest
- Pentest Guide
- How To Pentest A Network
- Pentest Open Source
- Pentest Tools For Windows
- Pentest App
- Pentest With Metasploit
- Hacker Computer
- Hacking Link
- Hacking Health
- Pentest +
- Pentest Magazine
Tuesday, June 9, 2020
WPSeku V0.4 - Wordpress Security Scanner
Aircrack-ng: The Next Generation Of Aircrack
 "Aircrack-ng is an 802.11 WEP and WPA-PSK keys cracking program that can recover keys once enough data packets have been captured. It implements the standard FMS attack along with some optimizations like KoreK attacks, as well as the all-new PTW attack, thus making the attack much faster compared to other WEP cracking tools. In fact, Aircrack-ng is a set of tools for auditing wireless networks." read more...
"Aircrack-ng is an 802.11 WEP and WPA-PSK keys cracking program that can recover keys once enough data packets have been captured. It implements the standard FMS attack along with some optimizations like KoreK attacks, as well as the all-new PTW attack, thus making the attack much faster compared to other WEP cracking tools. In fact, Aircrack-ng is a set of tools for auditing wireless networks." read more...Website: http://www.aircrack-ng.org


